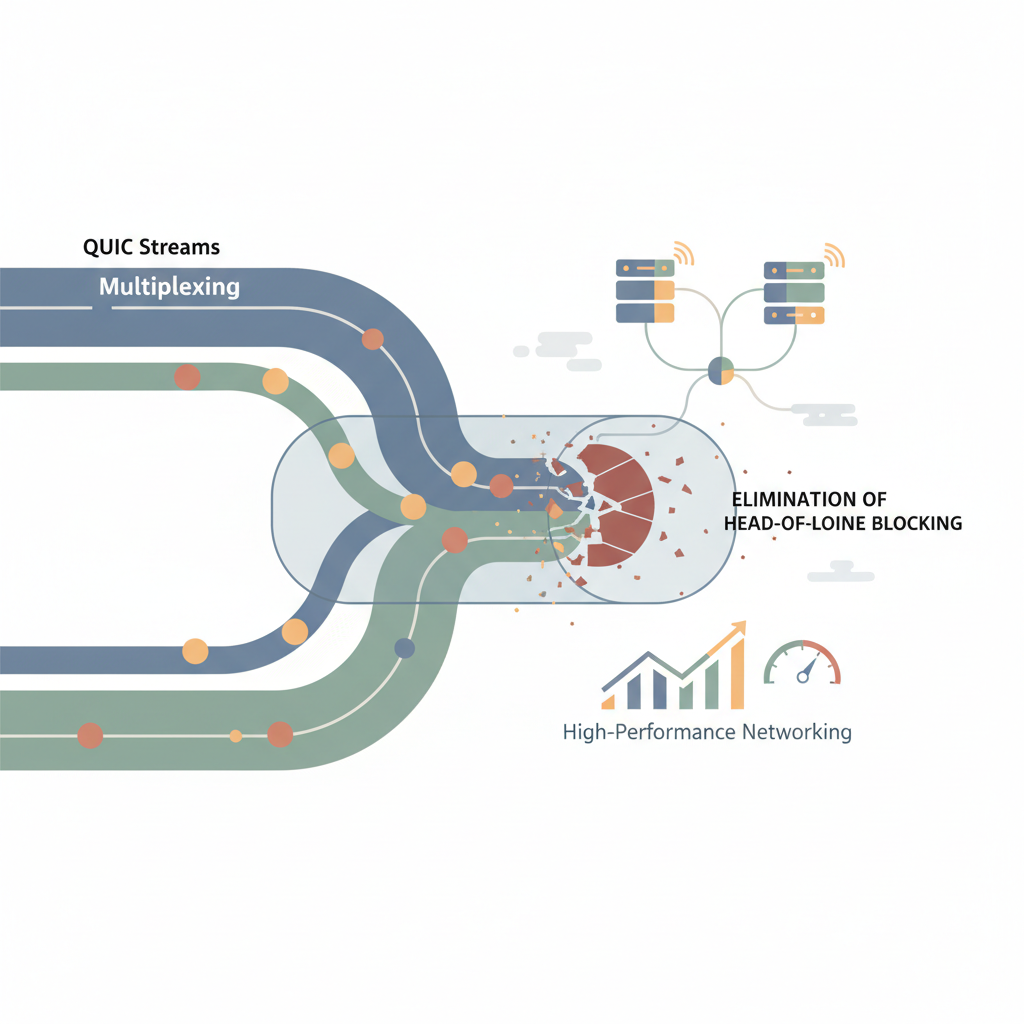
Deep Dive into QUIC Stream Multiplexing: Eliminating Head-of-Line Blocking for High-Performance Networking
A practical guide to QUIC’s stream multiplexing, showing how it solves head‑of‑line blocking and how to implement it in real systems.
A practical guide to QUIC’s stream multiplexing, showing how it solves head‑of‑line blocking and how to implement it in real systems.

A deep dive into MDM architecture, security controls, and lifecycle automation, illustrated with real‑world patterns from Intune, Android Enterprise, and Apple Business Manager.

A step‑by‑step guide that shows engineers how to run a quantized Llama model inside the browser using WebGPU, with code snippets, performance data, and production‑ready patterns.

A deep dive into implementing OpenTelemetry propagation, understanding header formats, and designing architectures that preserve trace continuity in distributed systems.
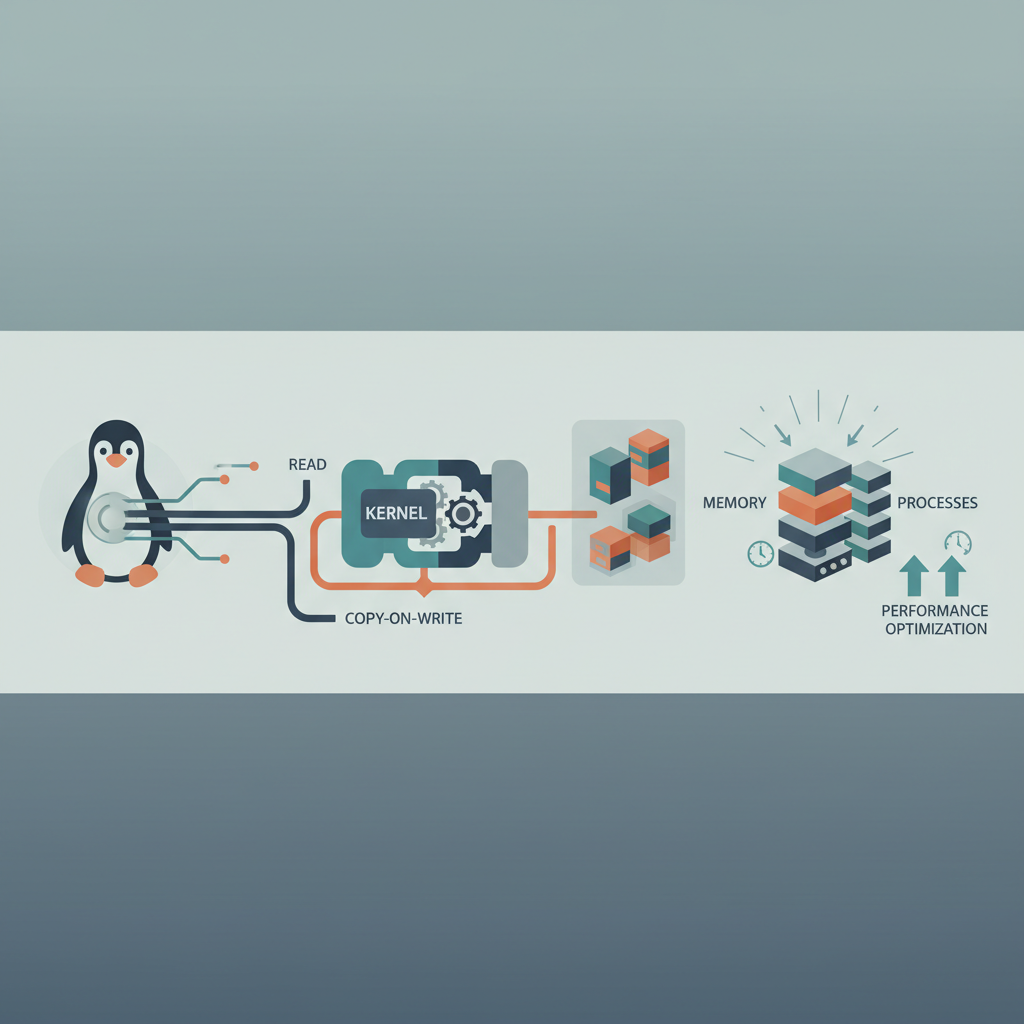
A technical walkthrough of Linux COW, covering kernel architecture, fault paths, and proven tuning patterns for real‑world services.