
Deep Dive into Flame Graphs: Visualizing Performance Bottlenecks and Identifying Hidden Execution Latency
A practical guide that walks engineers through generating, interpreting, and operationalizing flame graphs for real‑world systems.

A practical guide that walks engineers through generating, interpreting, and operationalizing flame graphs for real‑world systems.

A practical guide that walks you through cgroups v2 hierarchy, CPU, memory, and I/O controllers, and production‑ready patterns for resource isolation.

A deep dive into cgroups v2 architecture, practical commands, and performance‑tuning tricks you can apply today to keep containers and services well‑behaved in production.

A deep dive into cgroups v2 resource isolation, covering architecture, real‑world configuration, and performance tuning for production systems.
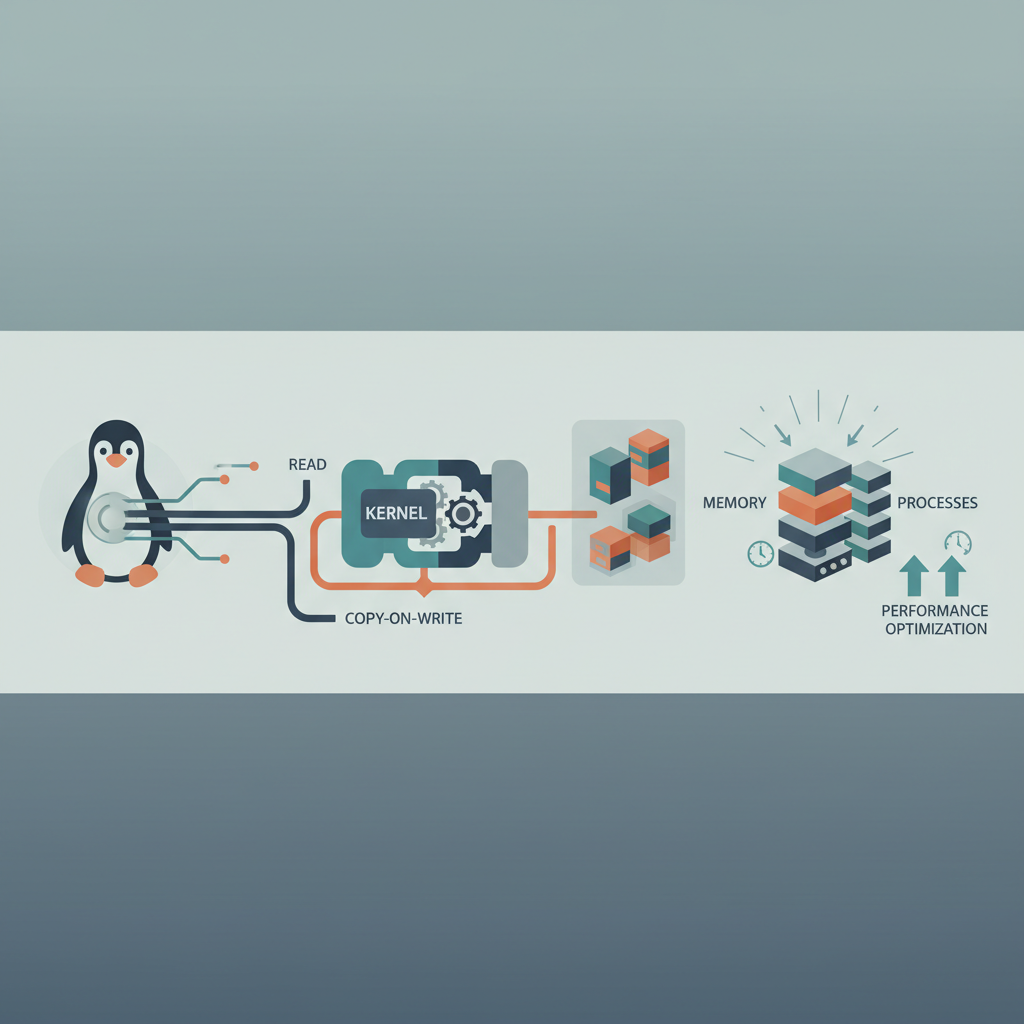
A technical walkthrough of Linux COW, covering kernel architecture, fault paths, and proven tuning patterns for real‑world services.